A terrifying new mobile malware trend is exploding, and it’s not after your passwords—it’s after your face. A sophisticated trojan called GoldPickaxe is making waves, specifically designed to steal facial recognition data from both iPhone and Android users. This isn’t just another tech scare; it’s a fundamental shift in mobile security threats.
I know it sounds like something out of a sci-fi movie, but the threat is very real. Cybercriminals are using this stolen biometric data to authorize fraudulent bank transactions, effectively becoming you.
Why GoldPickaxe Is Trending Now
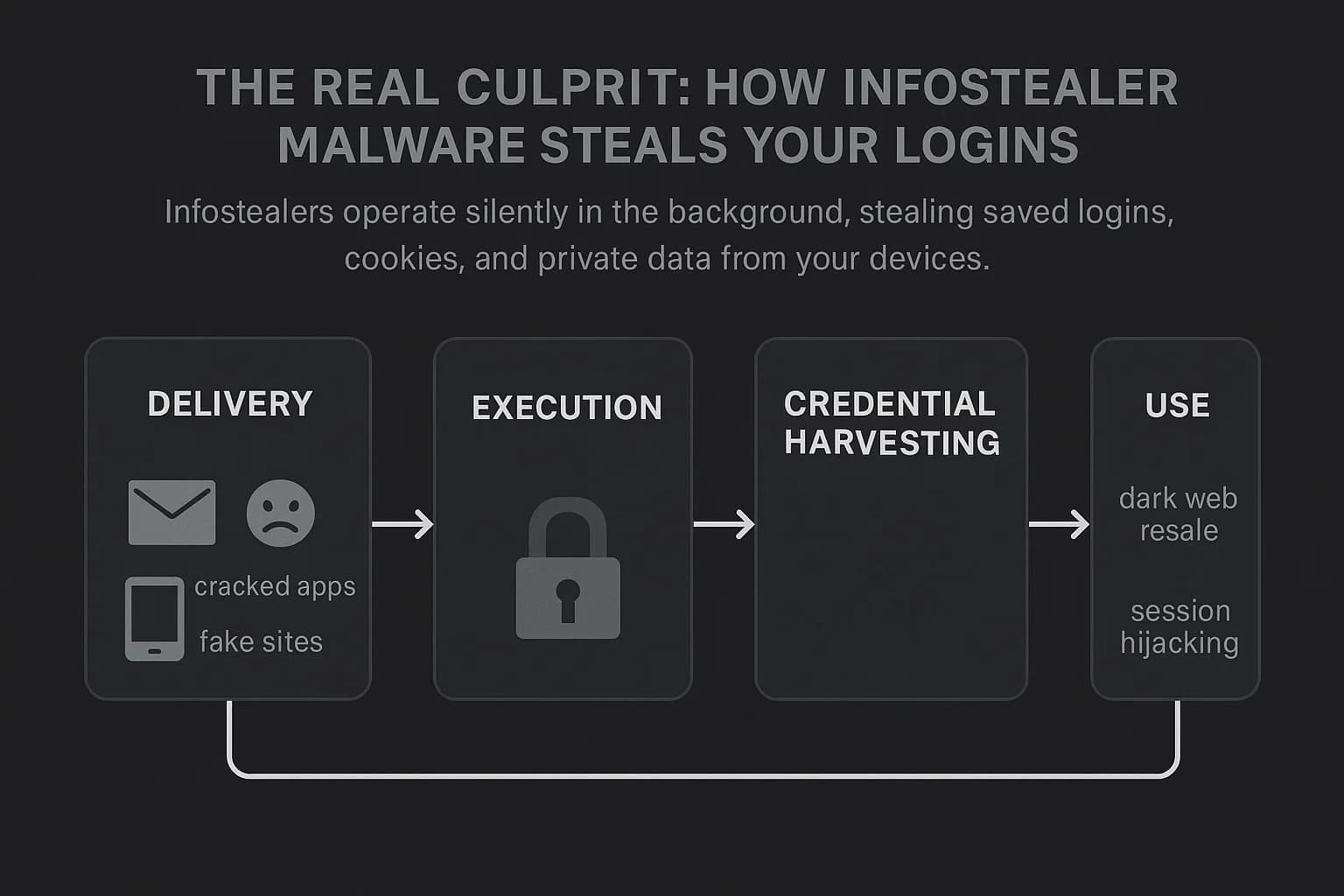
This malware is gaining so much attention because it bypasses traditional security. Instead of just stealing what you type, it steals who you are. The GoldPickaxe trojan tricks users into installing a fake app, often disguised as a government or utility service. Once installed, it prompts you to scan your face and upload your ID, gathering all the data it needs.
A group known as GoldFactory is reportedly behind this, and they’ve been refining their tactics. They use the stolen facial scans and AI-powered face-swapping services to create deepfakes, fooling banking apps that rely on biometric verification.
The scary part? It works on both Android and iOS. While Android versions have more extensive capabilities, the iOS version uses clever tricks involving Apple's TestFlight platform or by tricking users into installing a Mobile Device Management (MDM) profile, which gives the attacker significant control over the device.
How The Attack Works
Here’s a simplified breakdown of the GoldPickaxe scheme:
| Stage | Action | User Impact |
|---|---|---|
| 1. Lure | User receives a phishing message (smishing) via an app like LINE. | Message appears to be from a trusted government or financial institution. |
| 2. Installation | User is directed to a website to install a malicious app. | On iOS, this might involve installing a TestFlight app or an MDM profile. |
| 3. Data Harvest | The app requests a facial scan and a photo of the user's ID. | The malware also intercepts SMS for two-factor authentication codes. |
| 4. Fraud | Attackers use the data and deepfakes to access bank accounts. | Unauthorized transactions and financial loss. |
Common Mistake: Blindly Trusting App Prompts
The biggest failure point for users is social engineering. People are conditioned to follow prompts from apps that seem legitimate. The attackers exploit this trust masterfully. Just because an app asks for your face scan doesn't mean it's for a legitimate security check. This is a crucial vulnerability to understand, as even the most secure phones can be compromised if the user grants the necessary permissions. For anyone concerned about their device's integrity, learning about security tools like Apple's Lockdown Mode is a smart move.
This new wave of attacks highlights a growing problem with mobile security. As we rely more on biometric authentication, criminals will continue to find new ways to exploit it. The conversation is shifting from just protecting passwords to safeguarding our very identity. With threats evolving, understanding the core differences and security models of iPhone vs. Android can help you make more informed decisions.
If you suspect your device is compromised, don't wait. There are guides that can walk you through securing your device, like learning how to reset an Android phone to factory settings. The rise of new phone malware that uses AI is a clear sign that these threats are becoming more sophisticated.
Final thoughts
The GoldPickaxe trojan is a wake-up call. It's the first widely-reported iOS trojan that goes after biometric data this aggressively, and it signals a dangerous new frontier in cybercrime. Expect to see more malware families adopt these AI-driven techniques. The future of phone security will involve a greater focus on detecting and blocking social engineering attempts and educating users to be more skeptical of requests for sensitive biometric information. For now, the best defense is vigilance: be extremely cautious about what you install and the permissions you grant.